Searching For- Will1869 In-all Categoriesmovies... May 2026
Search complete. 0 results found.
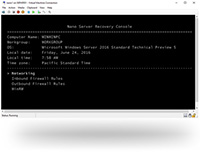
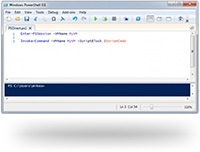
When we search for "Will1869" in All Categories , we are not searching for a movie. We are searching for a digital ghost. We are hoping that the metadata attached to an .mkv or .mp4 file contains a clue: a comment in the encoder's notes, a watermark from a release group, or a private tracker’s internal log. Will1869 could be the original uploader, the person who ripped the Blu-ray, or the owner of the hard drive where the file was last indexed. Why "Movies"? The search is constrained to the cinematic category, but that is a false constraint. A movie is a vessel. Inside that vessel could be anything: a forgotten indie film, a 4K restoration of a classic, or a home video mislabeled as a feature. By searching "All Categories" but specifically noting "Movies," the query admits its own desperation. The user is willing to look through music, software, and e-books, but they suspect the answer lies in cinema. Searching for- Will1869 in-All CategoriesMovies...
Cinema is time-bound. A film from 1994 feels different from a film from 2013. If Will1869 uploaded The Matrix in 2002, that tells us something about his taste. If he uploaded Gone with the Wind in 2020, that tells us something else. The movies themselves become a biographical sketch. We are not searching for a file; we are searching for a fingerprint left on culture. The most poignant part of the query is the trailing punctuation: "Movies..." Those three dots (an ellipsis) signify a loading state, a pause, an ongoing process. In user interface design, the ellipsis indicates that the system is thinking. But for the human waiting, it is a moment of pure potential. Will the search return zero results—the cold digital void of "404 Not Found"? Or will it return a single, mysterious file named will1869_final_cut_v3.mp4 ? Search complete
But the search itself was the story. If you intended this to be a factual lookup (e.g., identifying a specific actor, director, or film title "Will1869"), please clarify, and I will provide a factual research essay instead of a philosophical one. We are searching for a digital ghost
These words, stark against a plain background, represent the modern digital condition. They are the output of an automated process—likely a media server like Plex or Jellyfin, or a legacy torrent client trying to resolve a corrupted metadata file. But to the human eye, they read like an incantation. They are a digital séance. We are not merely looking for a file; we are searching for a person, a timestamp, and a story buried under layers of ones and zeros. The string "Will1869" is an artifact. The first part, "Will," suggests a given name—William, Willard, or simply a declaration of volition. The suffix, "1869," is a number without immediate context. It is not a standard birth year (that would make the person over 150 years old). It could be a street address, a locker combination, a historical reference (the completion of the Transcontinental Railroad, the death of James Prescott Joule), or simply the random digits a teenager appended to an email address in 1999 to satisfy a "unique username" requirement.
We search for "Will1869" because we have all been Will1869. We are all usernames attached to forgotten files, hoping that someone, someday, will query our metadata and wonder who we were. The search bar is not a destination; it is a Ouija board. And in the category of Movies, we are not looking for films. We are looking for proof that our digital selves leave traces behind.
Search complete. 0 results found.
When we search for "Will1869" in All Categories , we are not searching for a movie. We are searching for a digital ghost. We are hoping that the metadata attached to an .mkv or .mp4 file contains a clue: a comment in the encoder's notes, a watermark from a release group, or a private tracker’s internal log. Will1869 could be the original uploader, the person who ripped the Blu-ray, or the owner of the hard drive where the file was last indexed. Why "Movies"? The search is constrained to the cinematic category, but that is a false constraint. A movie is a vessel. Inside that vessel could be anything: a forgotten indie film, a 4K restoration of a classic, or a home video mislabeled as a feature. By searching "All Categories" but specifically noting "Movies," the query admits its own desperation. The user is willing to look through music, software, and e-books, but they suspect the answer lies in cinema.
Cinema is time-bound. A film from 1994 feels different from a film from 2013. If Will1869 uploaded The Matrix in 2002, that tells us something about his taste. If he uploaded Gone with the Wind in 2020, that tells us something else. The movies themselves become a biographical sketch. We are not searching for a file; we are searching for a fingerprint left on culture. The most poignant part of the query is the trailing punctuation: "Movies..." Those three dots (an ellipsis) signify a loading state, a pause, an ongoing process. In user interface design, the ellipsis indicates that the system is thinking. But for the human waiting, it is a moment of pure potential. Will the search return zero results—the cold digital void of "404 Not Found"? Or will it return a single, mysterious file named will1869_final_cut_v3.mp4 ?
But the search itself was the story. If you intended this to be a factual lookup (e.g., identifying a specific actor, director, or film title "Will1869"), please clarify, and I will provide a factual research essay instead of a philosophical one.
These words, stark against a plain background, represent the modern digital condition. They are the output of an automated process—likely a media server like Plex or Jellyfin, or a legacy torrent client trying to resolve a corrupted metadata file. But to the human eye, they read like an incantation. They are a digital séance. We are not merely looking for a file; we are searching for a person, a timestamp, and a story buried under layers of ones and zeros. The string "Will1869" is an artifact. The first part, "Will," suggests a given name—William, Willard, or simply a declaration of volition. The suffix, "1869," is a number without immediate context. It is not a standard birth year (that would make the person over 150 years old). It could be a street address, a locker combination, a historical reference (the completion of the Transcontinental Railroad, the death of James Prescott Joule), or simply the random digits a teenager appended to an email address in 1999 to satisfy a "unique username" requirement.
We search for "Will1869" because we have all been Will1869. We are all usernames attached to forgotten files, hoping that someone, someday, will query our metadata and wonder who we were. The search bar is not a destination; it is a Ouija board. And in the category of Movies, we are not looking for films. We are looking for proof that our digital selves leave traces behind.


 CyberStore WSS Datasheet
CyberStore WSS Datasheet  Cam Academy Trust Hyper-Converged Storage
Cam Academy Trust Hyper-Converged Storage 

















 Extensive Testing
Extensive Testing Customization Service
Customization Service


 Call Our US Sales Team Now
Call Our US Sales Team Now